Agents You Can Trust

Recognition
"The platform delivers two key outcomes: vulnerability prioritization and remediation, and is well positioned to solve both effectively."
James Berthoty, Founder at Latio
Read the full report →Meet your Agents
Each agent has a defined role and success metrics. Each gets the context to do its job: your scanner results, your code, your environment. Each is evaluated by our team before it joins yours.

Intelligence
Vulnerability Researcher
Meet Cassandra
Researches every CVE and encodes its applicability conditions. Powers the rest of the Konvu Agents.
Learn more →
Triage
Application Security Engineer
Meet Argus
Reads your code and your dependencies. Confirms which SAST and SCA findings are actually exploitable in your environment. Dismisses false positives with reasoning.
Learn more →
Triage
Cloud Security Engineer
Meet Nyx
Triages cloud security findings against your actual workloads, runtime, and configuration.
Learn more →
Remediation
Remediation Engineer
Meet Patcheus
Ships dependency upgrades and security fixes as pull requests. Lives in your Slack.
Learn more →
Offense
Pentester
Meet Hermes
Reproduces vulnerability reports end-to-end. Triages external reports, or confirms that fixes actually work.
Learn more →
Containment
Mitigation Engineer
Meet Aegis
Writes and deploys WAF rules to block exploitable vulnerabilities in minutes, closing the exploit window while the real fix ships.
Learn more →- +90%
- Average noise reduction
Fortune 500 Retail
Security Lead
Konvu gave us clarity. It dismissed the non exploitable findings and put the real risks at the top of the list.
- 3x
- Faster MTTR on real issues
Fintech SaaS
CISO
“We went from drowning in Snyk alerts to having a clear, prioritized view of what actually matters.”
- 93%
- Learn how a retail giant with 80k+ employees transformed their vulnerability management by automatically triaging Black Duck Polaris findings with AI-powered evidence.
Enterprise ready
Run on our cloud or yours. Compliant, configurable, and built to fit your security posture.
Cloud or self-hosted
Run on Konvu Cloud or deploy within your own infrastructure. Your code never leaves your building.
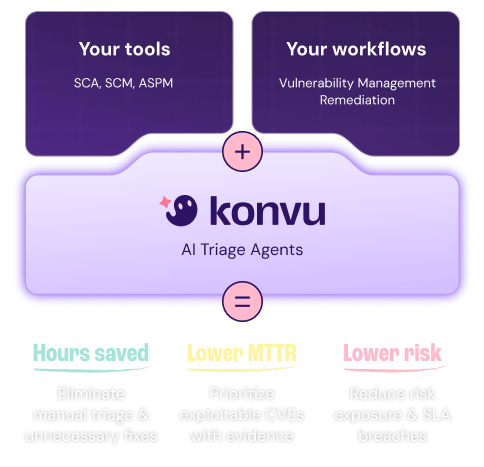
Frictionless integrations
Connects to your existing toolchain in minutes. Need an integration we don't have yet? We'll build it.
SOC 2 Type II
Independently audited and certified for security, availability, and confidentiality controls.
Configurable policies
Adapt to any workflow and regulatory environment. Define custom rules and enforce them automatically.
Privacy by design
Code is never stored by Konvu or model providers. Never used for training. Privacy guaranteed.
Expert-led support
From onboarding to deployment at scale, our team works alongside yours to ensure long-term success.
Latest from our blog
View all articles
How to Scale Vulnerability Triage Without Breaking Audit Requirements
Vulnerability volumes exceed human triage capacity, but auditors demand every finding accounted for. Evidence-based triage bridges the gap between scale and compliance.
Read
Why Static Code Reachability Is Not Enough: From "Reachable" to Truly Exploitable
Learn why static code reachability isn't enough for AppSec and how exploitability analysis slashes false positives and turns scanner noise into real risk.
Read
The Future of Vulnerability Management
For the past decade, security measured progress by vulnerability count. Detection wasn't progress, it was paralysis. Learn how agentic AI changes everything.
Read